Since AMREL customizes most of the products we sell, we pay pretty close attention to what our customers want. While we do not claim to be prophets, we have noticed certain trends when we discuss computing solutions with our clients. Here is what we think will be “The Next Big Things” for rugged computers.
Big displays/ Small form factors
We get a lot of inquires about the RF10, the only rugged laptop that has a 17” display. Same thing about our DK10 tablet that has a 12” display. Maybe it’s the popularity of mapping applications or maybe everyone is aging and getting poor eyesight. Whatever the reason, people want BIG screens.
At the same time, they want smaller form factors. People are using tablets for tasks that once required laptops, and are using handhelds for applications that once needed tablets. Please call us if you know how to put a 17” display on a smartphone.
ARM race
One key to the popularity of smaller from factors are ARM processors. While more limited in their ability to support full computer functions, they use less energy than traditional processors (such as Intel).
To get around the limitation of ARM processors, computing solutions have adopted “fat server/thin client” model. Computing functions are off-loaded to the cloud. You no longer need a powerful desktop computer to download your email. When your email is cloud based, a simple low powered smartphone can easily check it.
My smartphone, my trash
A consequence of the preference for ARM- based small form factors is that hardware is cheaper and more disposable. If your desktop computer is destroyed, you have not only lost an expensive piece of equipment, but also a lot of valuable data as well. If your smartphone gets trashed, it’s less expensive to replace, and your data lives on in the cloud.
Considering disposability is one of its main attractions, a smartphone that is also rugged may sound like a contradiction in terms. Even if it is relatively cheap to replace, a broken smartphone is still a time waster and a general pain in the rear end. So, we are getting many requests for durable handheld computers. In addition to the DB6, DF6 and our other established small platforms, we plan to soon launch a new line of super-tough handhelds.
Android rules, but mobile Windows is not dead yet
Android OS is clearly on the rise. Interestingly, this has not slowed down inquires to AMREL for Windows CE-based platforms. Institutions with legacy applications haven’t jumped on the Android bandwagon yet. While continuing to support mobile Windows OS, we plan to dramatically expand our Android offerings in the near future.
Attack of the super-thin computers
As you probably noticed, thin is in. Leaf through any computer magazine, and you will see ads boasting of their slim platforms. While this is primarily a phenomenon of consumer electronics, even the rarefied world of rugged platforms has been affected by “computer anorexia.”
Never one to pass up a good trend, AMREL offers:
• RS11 – With a 13” display, it’s the thinnest rugged laptop in the world
• DB6 – The super lightweight handheld
• RV11 – It is the thinnest rugged laptop with a 15” display on the market
This year we plan to offer a rugged tablet so thin you can cut cheese with it. Well, maybe not that thin, but still…
COTS, COTS, and more COTS
Classify this trend as “more of the same.” One of the biggest consumers of rugged platforms is the US Department of Defense (DOD). They have been COTS obsessed for years, and there is no sign of this mania letting up. COTS products are supposedly cheaper, have better supply lines, and the DOD doesn’t have to worry about keeping their production capabilities alive in times of low demand.
Of course the DOD still hasn’t lost its taste for highly specific requirements. This has led to the phenomena of “Customized COTS,” i.e. off-the-shelf products that can be easily modified. For almost 30 years, AMREL has pioneered “Customized COTS” and continues to be a leader in this field.
Quick & inexpensive prototyping
Incorporating end-user feedback for rugged solutions has always been problematic. With the pace of technological change rapidly accelerating and the increasing uncertainty surrounding possible future wars, adaptability has become ever more critical. Rugged solutions must be designed to be easily and inexpensively modifiable. Since customization is one of AMREL’s core capabilities, we feel very confident in meeting this challenge.
What do you think?
The above list is not be meant to be exhaustive, but just an informal collection of our impressions. What is your vision of the future of rugged computers? Send your thoughts to editor@amrel.com.
Learn more about AMREL’s offerings at computers.amrel.com



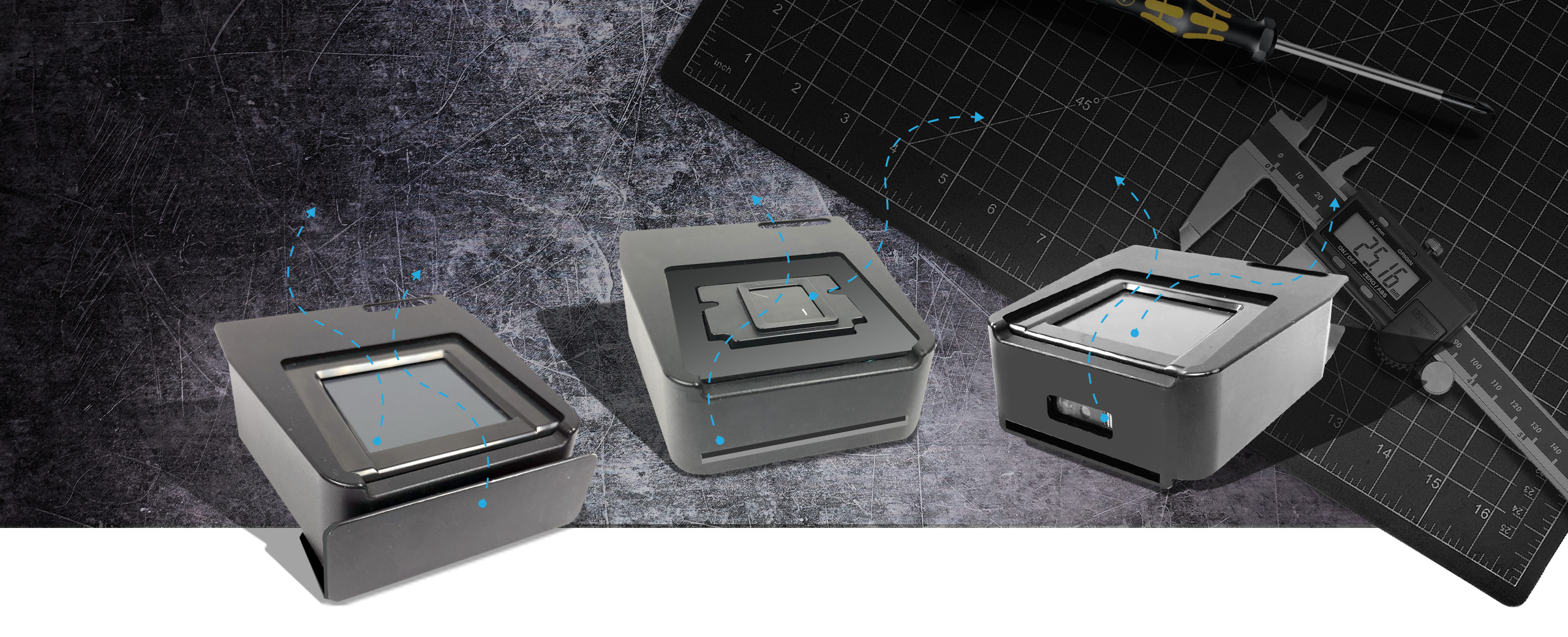
















 AMREL announces the launch of ROCKY DF6, a fully rugged handheld that’s small on Size, Weight, and Power (SWaP) requirements, but big on options. This is AMREL’s fourth generation of embedded products.
AMREL announces the launch of ROCKY DF6, a fully rugged handheld that’s small on Size, Weight, and Power (SWaP) requirements, but big on options. This is AMREL’s fourth generation of embedded products.
 You may not have had a chance to see AMREL’s new interoperability capability at AUVSI, but you can read about it on your free download. Just as our Flexpedient® technology revolutionized OCUs for UGVs, we think interoperable Small Lightweight Expansion Devices (SLED) will become standard for handheld applications. Click
You may not have had a chance to see AMREL’s new interoperability capability at AUVSI, but you can read about it on your free download. Just as our Flexpedient® technology revolutionized OCUs for UGVs, we think interoperable Small Lightweight Expansion Devices (SLED) will become standard for handheld applications. Click